A trusted automation tool has quietly become a weapon for delivering malware.
Researchers at Cisco Talos report that since at least October 2025, attackers have been abusing n8n workflows to bypass traditional security defenses. By leveraging the platform’s legitimate infrastructure and strong reputation, these campaigns can deliver tailored malware, establish persistent access, and fingerprint victims while evading detection.
What makes this tactic especially dangerous is how convincingly it blends into normal business activity. And because the attack adapts in real time to each victim, the same phishing link can lead to very different outcomes depending on who clicks it.
What is n8n, and how did it turn into an attack vector
n8n is a workflow automation platform that can integrate with APIs, including AI services.
Its ability to integrate with a wide range of applications and platforms has made it a popular choice for developers and anyone looking to automate their workflows end-to-end. It combines triggers, steps, and destinations to give users more control of their automation process, powered by any AI model.
To use the platform, users can either self-host n8n or register for a cloud-based account, in which they are assigned a subdomain ending in app.n8n.cloud. Everything a user does on their n8n account is run from this subdomain.
Here’s where the attackers come in.
Because n8n is popular and has a reputation as an AI automation tool like Zaiper, email servers, and even users tend to trust it inherently. That means fewer emails from its subdomain get blocked or sent to spam. Since it can send automated emails with higher deliverability, attackers have weaponized the platform to deliver malware via phishing emails to their targets.
What attacks were noticed
According to a threat spotlight report by Cisco Talos, emails containing n8n webhooks (automated flows) rose 686% in March this year compared to January 2025. While this could be attributed to a growing interest in n8n, the report also notes that increased malicious campaigns using n8n are driving this spike.
Malware delivery
The team, in their report, revealed that instead of delivering a single malware to every target, the attackers dynamically allocate payloads based on headers served from the webhook.
When a victim clicks the link bearing the malware, the webhook immediately reads the user-agent header. The webhook reads request headers such as the user-agent, allowing attackers to infer the victim’s browser and operating system. By reading that header information, the phishing operator can automatically tailor the payload. For example, what an iOS user gets will differ from what a Windows user gets, even if they both click the same link.
To make matters worse, n8n webhooks mask the source of the data they deliver. As a result, attackers use n8n as a relay tool, so the n8n trusted domain appears instead of their own malicious domain. Effectively, n8n becomes the middleman and public face of their malware campaign.
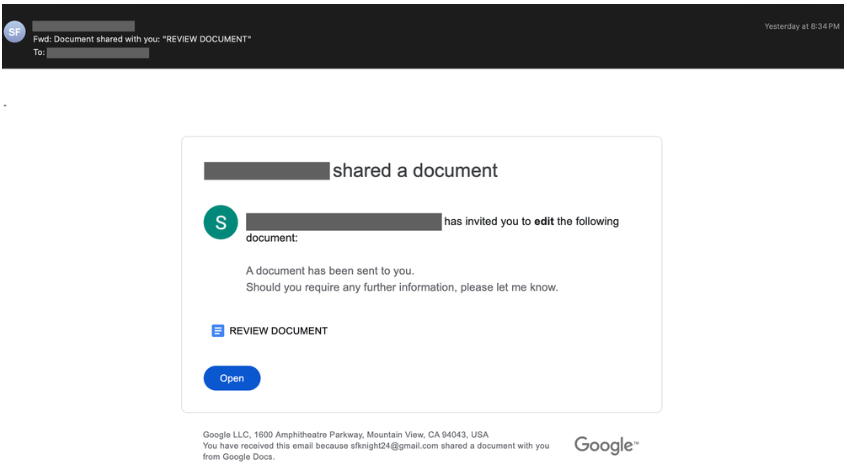
During their investigation, the team observed two campaigns. One delivered a Microsoft Windows Installer (MSI) file called OneDrive_Document_Reader_pHFNwtka_installer.msi. This Windows-focused payload installs a backdoor that allows it to exfiltrate data from its target’s device.
Another masquerades as a Microsoft OneDrive folder that, when clicked, downloads a payload, DownloadedOneDriveDocument.exe, which connects to a Command and Control (C2) server.
Device fingerprinting
Device fingerprints are unique identifiers used to persistently track a device across web sessions, even after a device has been wiped. Talos also found that attackers abusing n8n often fingerprint their victims. To do this, the attackers embed an invisible image in sent emails using CSS.
Although the image is invisible to the user, the email client sees it. In its attempt to load the image, it sends a request to the resource holding the image (the n8n subdomain), which logs the email address that made that request as active and a target for future attacks. After that, it responds with a URL bearing a tracking pixel.
What’s the way forward
In situations where legitimate platforms are abused, it becomes difficult to apply traditional defenses.
The research team offered a behavior-based detection. They also suggested threat intelligence among security platforms by sharing indicators of compromise (IOCs). To view the IOCs from this attack, check Talos’ GitHub repository. Security teams should also ensure robust email security systems are in place and, when necessary, flag emails from automation platforms for manual analysis.
On the user side, continued awareness about phishing techniques can do a lot of good because, at the end of the day, a successful phishing campaign still relies on its victim’s actions. And that action can be the difference between staying safe and compromising yourself.
For another example of how trusted platforms can become unexpected security risks, check out how a Salesforce misconfiguration exposed McGraw-Hill data and sparked claims that up to 45 million records were leaked.