A suspected North Korean operative attempted to infiltrate a cybersecurity firm using a stolen identity and an AI-generated resume, underscoring how hiring pipelines are becoming an attack vector.
The failed attempt reveals how threat actors are blending identity theft, automation, and anonymized infrastructure to bypass traditional recruiting safeguards.
“In June 2025, we used a combination of pre-employment OSINT due diligence and targeted interview questions to expose a suspected DPRK operative,” researchers said in their report.
Inside North Korea’s hiring fraud scheme
This incident is part of a broader campaign in which North Korean IT workers pose as legitimate remote candidates to secure employment and funnel earnings back to the regime.
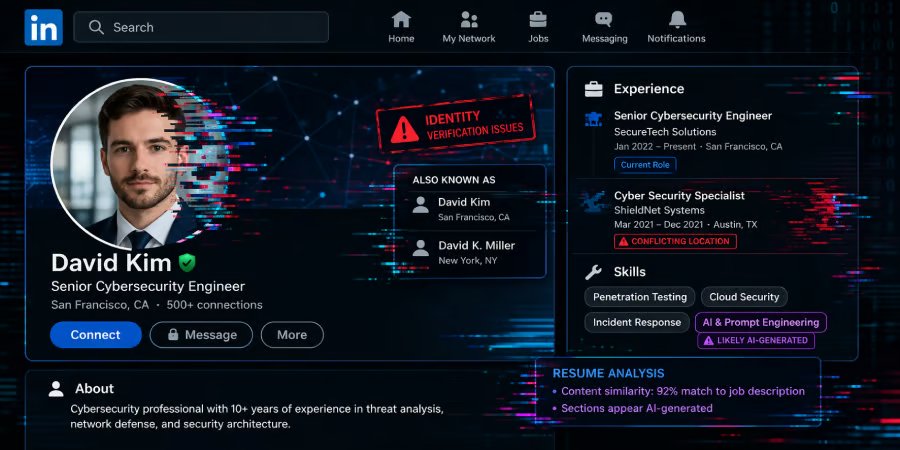
These operations follow a consistent set of tactics, including the use of newly created email accounts, stolen identities, fake LinkedIn and resume profiles, and AI-assisted content designed to pass automated screening systems.
The risk goes well beyond payroll fraud — once inside, these individuals can operate as insider threats with access to sensitive systems, enabling data exfiltration, intellectual property theft, and long-term persistence.
Organizations hiring remote technical talent, particularly for high-privilege or engineering roles, are especially vulnerable to this type of infiltration.
How attackers build credible identities
To establish credibility, the operative combined identity theft, AI-generated content, and anonymized infrastructure.
They used IP addresses associated with the Astrill VPN network and a VoIP phone number linked to a US location to reinforce a believable persona.
The resume itself closely mirrored the job description, copying required skills and responsibilities to pass keyword-based screening systems — a tactic increasingly used to bypass automated hiring filters.
Researchers also identified multiple resume profiles under the same name with conflicting details, suggesting the persona was reused and adapted across platforms to increase the chances of success.
Red flags during the interview process
Behavioral indicators during the interview further exposed the deception. The candidate frequently looked off-screen, likely relying on an AI chatbot for real-time responses, and struggled with unscripted or unexpected questions.
Despite claiming over a decade of experience, the individual could not provide verifiable work samples, had no GitHub or public portfolio, and ultimately ended the session abruptly when asked to demonstrate prior work — clear signs of fabricated experience.
Inside the laptop farm infrastructure
Further investigation revealed that the operation extended beyond a single applicant. A company-issued device was traced to a laptop farm environment, where multiple corporate laptops were clustered together and remotely controlled.
Investigators identified roughly 40 devices on the network, with approximately 20 likely part of the coordinated operation — highlighting the scale and industrialization of these schemes.
The setup leveraged PiKVM devices, enabling attackers to remotely control systems at the hardware level — even before the operating system loads — making detection more difficult than traditional remote access tools.
The infrastructure was further supported by mesh VPN services such as Tailscale, which enabled encrypted, peer-to-peer connections between devices and scalable, stealthy remote access across geographically dispersed locations. This combination of hardware-level control and secure networking creates a resilient environment for maintaining persistent access to enterprise systems while appearing to operate locally.
Mitigating insider threats in hiring
As hiring-related threats grow more sophisticated, organizations can no longer rely on traditional screening alone. Attackers are increasingly blending AI, stolen identities, and remote access techniques to bypass standard controls.
Defending against this requires a layered approach that spans pre-hire validation, technical controls, and ongoing monitoring.
- Conduct identity verification and OSINT checks to validate candidate identities, histories, and digital footprints.
- Verify the consistency of IP addresses, phone numbers, and geolocation to detect anonymization or location spoofing.
- Require live work demonstrations and use dynamic interview questions to expose AI-assisted or scripted responses.
- Monitor for inconsistent profiles, anomalous behavior, and indicators of shared or remotely controlled devices.
- Enforce least privilege, segment access for new hires, and restrict unauthorized remote access tools.
- Implement device controls and onboarding safeguards, including verified access, geolocation checks, and delayed provisioning.
- Regularly test incident response plans for insider threats, compromised accounts, and suspicious employee activity.
Together, these measures help organizations build resilience against evolving hiring threats while limiting exposure to insider-driven compromise.
Editor’s note: This article originally appeared on our sister publication, eSecurityPlanet.