A simple unpatched bug has led to a major breach, exposing millions of LexisNexis records.
According to BleepingComputer, a recent breach on LexisNexis gave hackers access to nearly 4 million database records, thousands of accounts, password hashes, and cloud records. The company admitted the hackers gained access by exploiting an unpatched React vulnerability in its systems.
The company, which provides legal and data analytics services to government and corporate organizations in more than 150 countries, saw more than 2 gigabytes of stolen data dumped on several dark web platforms by FulcrumSec, a hacker group.
From an unpatched vulnerability to a data breach
According to Automox, 60% of data breaches are tied to unpatched vulnerabilities. While others have slightly different statistics, the signal is clear: unpatched system flaws have been an easy way in for hackers. And LexisNexis is yet another number in the broader stats.
BleepingComputer reported that the hackers exploited a months-old vulnerability in React2Shell. The flaw enabled them to access AWS containers containing customer information. The hackers noted that the company, which also provides security services, had insecure AWS infrastructure, allowing them to gain easy access to data stored in its cloud account.
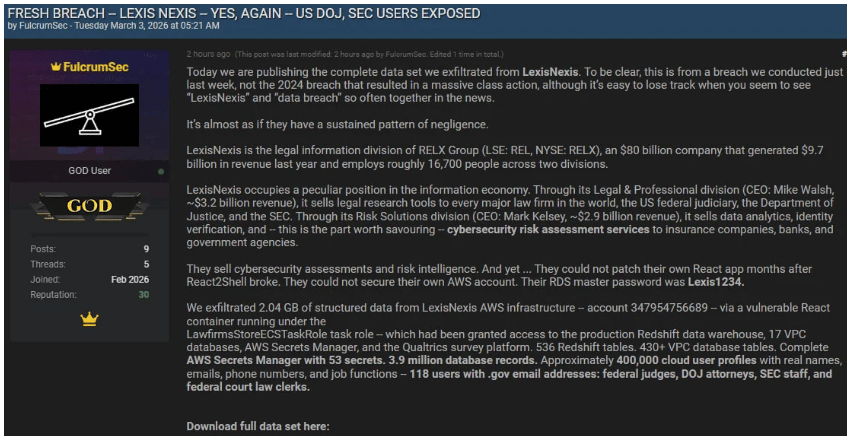
Although the vulnerability became public in 2025, and a patch was already available, the company continued running a React application on the vulnerable version.
In a post on the dark web, the hackers said their attempts to contact LexisNexis about the issue were unsuccessful as the company declined to work with them.
Exposed data, as cited by BleepingComputer, includes:
- 536 Redshift tables
- 430+ VPC database tables
- 53 AWS Secrets Manager secrets in plaintext
- 3.9M database records
- 21,042 customer accounts
- 5,582 attorney survey respondents
- 45 employee password hashes
- Complete VPC infrastructure mapping
What we know from the company
Admitting to the breach, the company announced that the effect was minimal. Speaking to BleepingComputer, a spokesperson for the company said:
“Our investigation has confirmed that an unauthorized party accessed a limited number of servers.” Confirming the scope and severity of the breach, the spokesperson also noted:
“These servers contained mostly legacy, deprecated data from prior to 2020, including information such as customer names, user IDs, business contact information, products used, customer surveys with respondent IP addresses, and support tickets.”
LexisNexis also said, “The impacted information did not contain Social Security numbers, driver’s license numbers, or any other sensitive personally identifiable information; credit card, bank accounts, or any other financial information; active passwords; or customer search queries, customer client or matter information, or customer contracts.”
So far, the company has contacted affected customers of the incident. LexisNexis also claimed it has informed law enforcement agencies about the breach. Additionally, it contacted an external cybersecurity company to investigate and contain the incident. The company also claimed the incident didn’t affect its business continuity.
What this breach shows
The attack on LexisNexis shows that most successful cyberattacks are often not new techniques. Instead, they happen due to basic failures to install critical software updates or configure solid infrastructure.
With data tied to thousands of government and Department of Justice employees exposed, the breach marks a notable hit on the legal sector through a weak point in a common supply chain. As with most incidents of this kind, affected customers are expected to receive guidance on steps they should take to protect their data.
Also read: Microsoft’s February Patch Tuesday fixes six zero-days under attack.


